Ongoing Sextortion Scam Leverages Hacked IoT Products, Bitcoin Ransom
Adrien Gendre
—August 09, 2018
—3 min read

Krebs on Security detailed a new sextortion scam on July 18, 2018, though initial reports began surfacing on Reddit as early as April. According to Krebs, “The message purports to have been sent from a hacker who’s compromised your computer and used your webcam to record a video of you while you were watching porn. The missive threatens to release the video to all your contacts unless you pay a Bitcoin ransom. The new twist? The email now references a real password previously tied to the recipient’s email address.”
Recipients of the scam told Krebs that the passwords referenced in the emails were close to ten years old, and that none had been used on their current computers. The age of the passwords should have tipped recipients off that hackers hadn’t, in fact, compromised their computers. However, the use of once-valid passwords, combined with the potential shame from having alleged porn watching (or worse) revealed to friends and acquaintances, was enough to lure some into paying the ransom.
Vade has blocked 600,000 sextortion scam emails since June
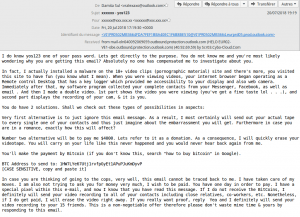
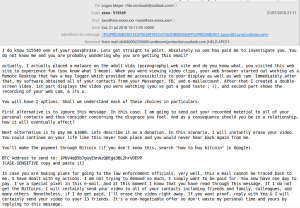
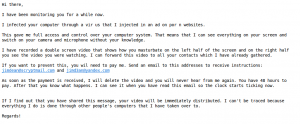
As Vade protects more than 500 million inboxes worldwide, including consumer email accounts through ISPs and telcos, we have seen this sextortion scam firsthand. In fact, since June, our filter engine has identified and blocked nearly 600,000 sextortion scam emails. The following are real examples that we blocked:
According to our analysis, the emails are originating from all over the world but 90 percent of the messages are in English, with a small percentage in poorly translated French. In most cases, hacked IoT products, cameras, routers, and websites are being used to send the emails. Hackers are using the command line in the Linux operating system used by these IoT products to send the emails, without needing a webmail client.
In addition, most of the sender addresses are random Hotmail or Outlook addresses that appear to be auto-generated. Here are a few examples:
- xcdesiraetu@outlook.com
- ddlillisymx@outlook.com
- pcmissylku@outlook.com
- sydcecilmlb@outlook.com
- ecnapoleonxua@outlook.com
- prshildagardxmi@outlook.com
- cldianemarieyrx@outlook.com
- qhmyrtieqe@outlook.com
- edtildaxmu@outlook.com
- ggjaribhfo@outlook.com
- hjotuanya@hotmail.com
For most of the 600,000 emails, the messages include a bitcoin address for the ransom payment. We developed a script to analyze a sample of the bitcoin addresses included in the emails we’ve analyzed. Based on this sample, a total of around $30,100 has been paid to date as ransom. Here’s one example of a payment of 0.12 BTC ($979) on July 25th.
Hackers continue to refine and iterate upon this sextortion scam
What’s perhaps most important to note is that the attack is ongoing and iterative. According to Sebastien Gest, Tech Evangelist at Vade who has been researching details on this scam, "We continue to see—and catch—new versions of these sextortion scam emails each day, thanks to our heuristic filters. The hackers appear to be analyzing the performance of their attack and tweaking the messages in an attempt to avoid detection by email security products like Vade."
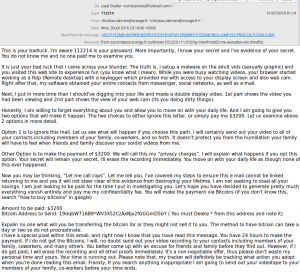
For instance, in this email, the hacker tried to obfuscate the blockchain address with an asterisk:
Here’s another example an email address was provided for the recipient to contact for payment instructions, rather than a blockchain address:
Krebs speculates that the hacker might also refine the sextortion scam by using more recent passwords — along with other personal data that can be found online — to make it even more convincing. According to the article, “An industrious scammer could simply execute this scheme using a customer database from a freshly hacked Web site, emailing all users of that hacked site with a similar message and a current, working password.”
Phishing surpasses ransomware as the top email threat of 2018
What’s abundantly clear is that while 2017 was the year of ransomware, 2018 will be the year phishing. In Q1, we discovered a massive phishing attack targeting 550 million email users globally. We also recently published our first-ever Phishers’ Favorites top 25 list, which showed that Microsoft Office 365-based phishing attacks increased 57 percent in Q2.
Whether you’re accessing your personal or professional email account, it’s critical to be more vigilant than ever. While end user training is one important piece of a sound email security strategy, predictive defense technology is another. A solution like Vade can help ensure sextortion scams and other phishing emails never reach the inbox in the first place.