Sophisticated, Simple Cybersecurity
Cyberattacks are constantly evolving, and Microsoft 365 has become a prime target for hackers. With Hornetsecurity, secure your emails, data, and organization with 365 Total Protection – an all-in-one solution that combines intelligent filtering, automated backup, and regulatory compliance.
Our ambition: To become the European Leader in Cybersecurity!
ONE TEAM – ONE BRAND
Since Hornetsecurity and Vade became the European Champion of Cybersecurity, many things have evolved. We have united our strengths by harmonizing our processes globally, leveraging our mutual experiences.
Now, let's move to the next step: becoming a single brand. One thing is certain: the colors have changed, the logo has changed, but our values remain the same – for our employees, customers, and partners. We continue to carry our passion for cybersecurity with excellence and innovation.
Email Security powered by AI
Smart cybersecurity for maximum protection
Hornetsecurity integrates advanced AI and automation to provide real-time protection against the most sophisticated cyber threats. Our 365 Total Protection solution secures your emails, data, and organization through proactive threat analysis, intelligent filtering, and automatic updates.
With machine learning and continuous user feedback, our AI engine instantly detects and blocks phishing attacks, ransomware, BEC, malware, and much more before they reach your inbox.
emails analyzed per day
items blocked by Computer Vision per day
algorithms updated per minute
365 Total Protection: Complete Security for Microsoft 365
Protect your business with an all-in-one solution that combines advanced cybersecurity, compliance, and service continuity for Microsoft 365.
In a world where cyber threats are constantly evolving, 365 Total Protection offers comprehensive and proactive protection to secure your emails, protect your data, and ensure regulatory compliance. Using AI-powered filtering technologies, this solution detects and neutralizes threats in real-time, before they reach your inbox.
With 365 Total Protection, enjoy an integrated and automated approach to strengthen your organization’s security, without added complexity.

Advanced email security, without compromise
Cybersecurity shouldn’t slow down your business. Hornetsecurity’s 365 Total Protection integrates natively with Microsoft 365, without modifying MX records or disrupting workflows.
- Real-time protection against phishing, ransomware, and advanced threats
- Securing links and attachments to block attacks before they reach users
- Centralized and automated management for MSPs and businesses, with integration to SIEM, XDR, and EDR solutions
- Fast deployment and simplified administration via a single portal.
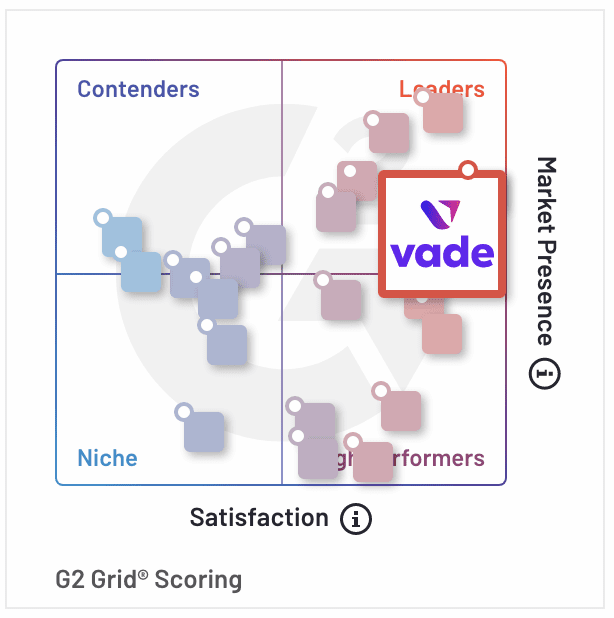
Recognized by G2
Hornetsecurity recognized by G2 as a Leader in Email Security and More
Hornetsecurity has been named a Leader in the G2 Grid® for Email Security, Cloud Email Security and Anti-Spam based on high customer satisfaction and substantial market presence.
Key takeaways:
- 100% of users rated it 4 or 5 stars
- 100% of users believe Hornetsecurity is headed in the right direction
- 97% of users said they would be likely to recommend Hornetsecurity