Apple and Amazon Invoice Scams Mimic Tech Support Scams
Natalie Petitto
—November 30, 2021
—2 min read

As holiday season approaches and shopping gets underway, online receipts are hitting inboxes around the world. Unfortunately, many are fake. New Apple and Amazon scams are making the rounds and luring users with high-dollar invoices for technology purchases.
The scams have eerie similarities to an ongoing tech support scam, first reported by Vade in April. In it, hackers spoof Norton, McAfee, and Microsoft, using fake invoices for antivirus subscriptions. As with the tech support scams, users who receive the fake Apple and Amazon invoices are instructed to call a phone number in the email footer to cancel their subscriptions.
According to Nicolas Joffre, Threat Intelligence and Response Center (TIRC) America Manager at Vade, “it's pretty much the same process as the tech support scam. The scammers use fear techniques and confusion to trick the victims into calling a toll-free number. The email usually shows what looks like an invoice of an important purchase.”
The invoices are, of course, fake, but when high-dollar invoices appear in users’ inboxes, users are certain to be alarmed and potentially vulnerable to calling the phone number to cancel the payment.
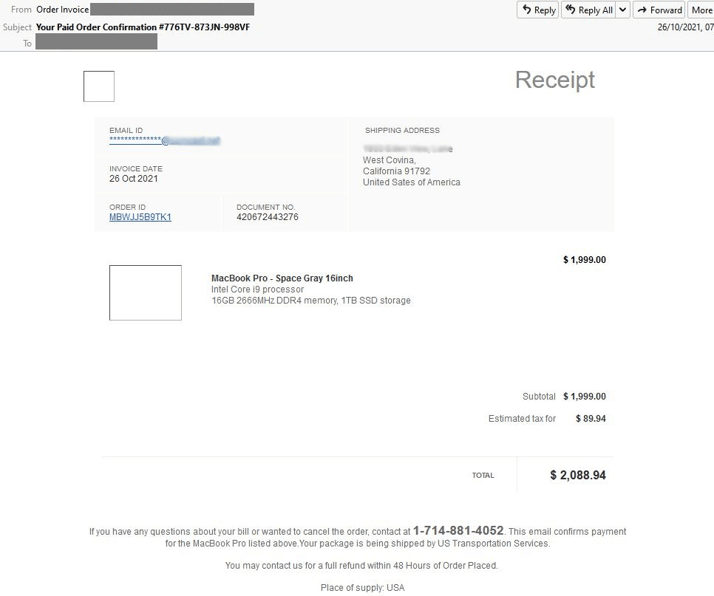
In the email footer is the note that users have only 48 hours to cancel their MacBook purchase over the phone. This adds a sense of urgency to what is already a worrisome message about a high-value purchase, a common psychological tactic used in both phishing and spear phishing.
Use of a phone number is smart for three reasons: First, there is no need for the hacker to build a phishing page; second, because the email includes no URLs, it can bypass an email filter; and third, the hacker has the opportunity to verbally manipulate and possibly threaten the person over the phone.
At the time of this writing, the phone number in the email footer was still in service, but we received no answer when we attempted contact. In the tech support scam, cybercriminals walk victims through the process of installing remote access software on their computers. This convinces them that their computers are infected with a virus, thus requiring the antivirus software subscription.
The Amazon invoice scam features two purchases, one for a subwoofer and another for a wireless headset. As with the Apple scam, the email includes a contact number but no other identifying features typical in phishing emails, such as URLs.
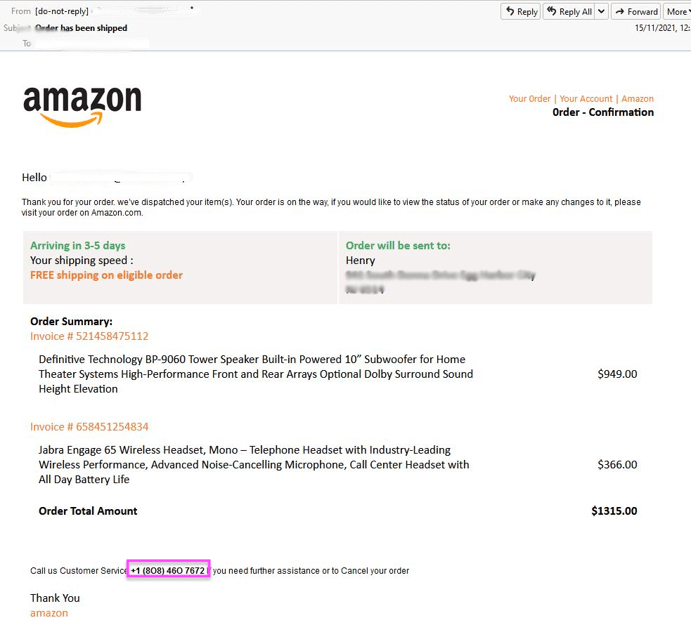
“The goal is to panic the victims into believing that someone has ordered an expensive item with their debit or credit card,” Joffre said. “Scammers are hoping that the victim will call the number to cancel the order. Once the victim calls the number, scammers usually pretend to be from the Amazon or Apple team. They will ask for personal details such as a name, address, and credit card number for ‘security reasons.’ The stolen information will then be used for fraud.”
Invoice scams spiked in mid-November
As you can see in the below image, Vade started tracking this scam in October 2021. By mid-November, less than two weeks before Black Friday, the scam surged to more than 60,000 emails in one day. Each email is unique, with random headers, senders, and subjects, so it is probable that the total amount of emails is higher than what you see in the chart.
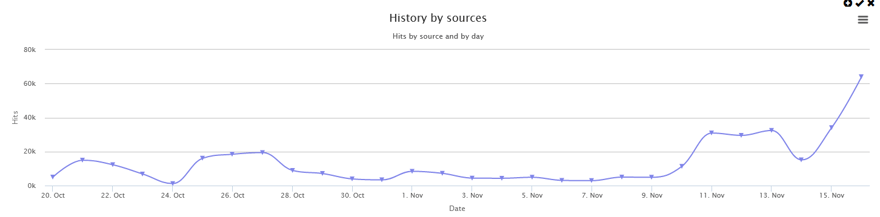
Because of the low numbers in mid-October and spike in mid-November, it is probable that scammers were testing their emails in advance of the holiday season. Black Friday, of course, kicks off the holiday shopping season in many countries throughout the world. Users receive receipt confirmations and invoices constantly throughout the holiday season, and they are likely keeping an eye on both purchases and shipping confirmations.
The missing links
Because the Apple and Amazon emails do not feature URLs, they are particularly difficult to detect. This is especially true if hackers are sending the emails from clean IPs and legitimate domains. Signature scanning, which analyzes URLs and code, is useless in this scenario and will not block the emails. Protecting users from these types of scams requires AI-based anti-phishing technology that analyzes not only signatures and reputations, but behavior, content, and context, the full scope of possibilities and scenarios.



