How Data Leaks Unleash Targeted Phishing Attempts
Adrien Gendre
—March 12, 2020
—4 min read

When a large data leak is reported in the news, most of us worry about highly sensitive data. But it’s not all about usernames and passwords. What many consumers don’t realize is that seemingly innocuous personal information can be used as leverage in phishing attempts and other targeted email attacks.
From the general interests you select when setting up a new account online to the security questions you create to protect those accounts, any type of leaked data can and will be used against you.
High-profile breaches inspire phishers to get to work
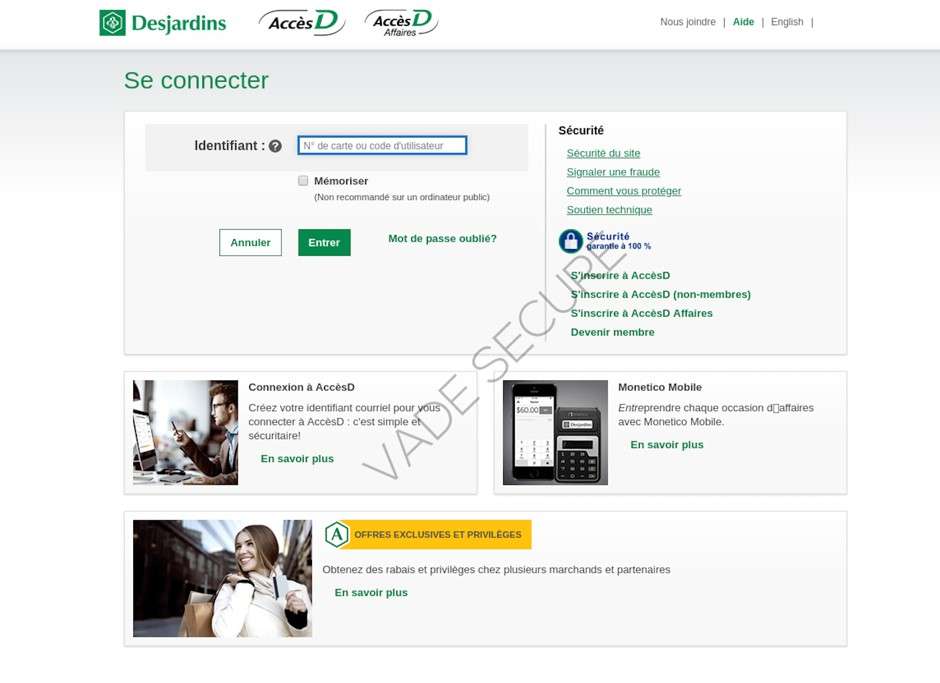
Desjardins Group, the largest credit union cooperative financial group in Canada and largest association of credit unions in North America, suffered a massive breach in June 2019. A Desjardins employee leaked the data of around 2.9 million Desjardins customers, including businesses. The employee was fired and arrested for the breach.
The leaked data included names, addresses, birth dates, social insurance numbers, and data about users’ transaction habits. The leaked data appeared on the dark web in late June. By August, the leak had cost Desjardins $53 million.
For some perspective on how data leaks kickstart phishing activity, consider how Desjardins went from the phishers’ ignore list to hit list in the last year: In 2018, Vade detected 255 unique Desjardins phishing URLs. In 2019, that figure jumped 1,680.4% for a total of 4,540 unique phishing URLs.
The Equifax data breach of 2017 was immediately followed by a warning about phishing attempts from the Federal Trade Commission (FTC). Shortly after the breach, Equifax set up a website where users could enter personal information to determine if their data was compromised in the breach. To demonstrate the insecurity of the website, a developer scraped the code from the Equifax website and built an identical phishing page, which included an SSL certificate. The page was so convincing that Equifax, already under fire for its response to the breach, tweeted the URL of the fake phishing page to its followers—no less than three times.
The above example is unique because in the case of such a high-profile breach, hackers didn’t need to be in possession of any sensitive data—they could rely on consumers to come to them, rather than the other way around with a phishing email.
Phishing attempts related to Equifax were detected throughout 2017 and 2018, with affected breach victims on high alert and susceptible to phishing emails featuring security alerts from banks. In 2018, Vade detected 38,537 unique phishing emails targeting top banks, including Bank of America, Wells Fargo, and Chase.
Security questions are an entryway into password-protected accounts
Recovering a password is often as simple as answering a few security questions that you selected at the time of account creation, such as the city where you were married, the name of your first pet, or the make and model of your first car. If that information is leaked, a hacker can access your account without ever entering your password.
In 2018, security analyst, Brian Krebs, detailed the many variations of the “secret questions” consumers answer on informal surveys, particularly on social media sites like Facebook. These historic details, Krebs said, are an invitation for hackers to gain backdoor access to your accounts. For example, questions related to the make and model of your first car, Krebs says, is often one of the first questions you encounter when setting up an online banking account.
Historic details also provide the ammunition necessary to carry out targeted phishing and spear phishing attacks. Knowing your personal interests helps a phisher determine what types of phishing emails you’re likely to respond to, and it makes it easier for a spear phisher to impersonate someone you know.
Personal leaks fuel phishing attempts from fake social profiles
Your personal data is more than your username, password, and credit card number. It could also include your political affiliation, hobbies, general interests, and even your purchasing habits. With this information in hand, hackers create virtual profiles of breach victims and use them to target new victims.
In October 2019, Wired reported that some 1.2 billion such records were discovered on an unsecured server. The data trove included the personal data of hundreds of millions of users from Facebook, Twitter, LinkedIn, and GitHub. While it’s easy enough to create a fake social media account, being in possession of this much personal data reduces the level of effort required to create a fake profile and adds a level of authenticity that would be difficult to achieve with a purely fictional profile.
In 2017, Israel Defense Forces (IDF) identified a Hamas network targeting Israeli soldiers. Hamas created fake profiles of women on social media using leaked data, including personal photos. Three such honeypot scams were discovered by IDF from 2017 to 2020. In the most recent scam, Hamas first corresponded with the soldiers by phone to lure them in, then invited them to private social networking apps via a phishing URL. Once downloaded, the apps unleashed a virus that took control of the soldiers’ phones, giving Hamas access to the phones’ cameras and microphones, the soldiers’ locations, and more.
Leaked data is a double-edged sword in extortion scams
Hackers have been getting creative with extortion attempts, particularly when it comes to leveraging leaked data to get their victims to comply. 2019 saw a resurgence of phishing-related ransomware attacks that crippled businesses around the world. In most ransomware cases, hackers threaten to destroy a business’s data if their demands are not met. Recently, they’ve shifted gears and threatened to leak the data.
This tactic is also used in GDPR blackmail. In the event of a data breach, businesses operating under GDPR face a $20 million fine or 4 percent of the company’s revenue. Like the example above, instead of encrypting a business’s data, hackers demand a Bitcoin payment to avoid seeing the data leaked on the internet. Known as a “ransomhack,” GDPR blackmail demands are typically between $1,000 and $10,000—next to nothing compared to a GDPR fine.
Finally, sextortion emails become all the more convincing, and scary, when a hackers uses deeply personal data against their victim. In January 2020, Vade discovered an extortion scam targeting victims of the 2015 Ashley Madison data breach. The extortion email was highly personalized with the victim’s personal data, including bank account information, telephone number, birth date, security questions, private messages, and even personal “preferences” the victim selected when creating their Ashley Madison account.
The 2015 Ashley Madison leak exposed the personal data of more than 32 million users. The above example targeted an average user, but it’s not a stretch to say that some users were more than average. In 2015, Wired reported that around 15,000 Ashley Madison accounts used .gov or .mil email addresses. It’s unclear if the government email addresses were legitimate, but it requires only a limited imagination to consider the lengths to which powerful people might go to make an extortion attempt go away.
Protecting yourself from data leaks
More than 7.9 billion records were exposed in 2019. Unless you are extremely lucky or extremely offline, then your own data is likely among them. Fortunately, there are ways to protect yourself from phishing attempts both before and after a data leak:
- Use two-factor authentication with an OTP (one-time password) app. Google Authenticator and Microsoft Authenticator are two excellent options.
- Update your security parameters at least twice per year in your email and online accounts.
- Monitor your personal data on a regular basis. Third-party websites like haveibeenpwned.com and breachalarm.com will search for compromised information based on your email address. You can also sign up for alerts.



