Keylogger Attacks: What They Are and How to Prevent Them
Adrien Gendre
—March 02, 2023
—3 min read
Keylogger attacks use a common and especially invasive type of malware to exploit victims. From harvesting user credentials to facilitating account takeover, multi-phase attacks, and more, keyloggers pose a critical threat to businesses of all sizes.
Read on to learn more about keylogger attacks, including the most common types, how they’ve evolved over the years, and how your organization can prevent them.
What are keylogger attacks?
Keylogging, or keystroke logging, is a tool used by cybercriminals to track and record a user’s computer activity to gain access to sensitive information. A form of spyware, they record every keystroke made by a user. Cybercriminals launch attacks to steal user credentials, record sensitive information such as credit card numbers, track online browsing activity, and more.
Types of keyloggers
Keyloggers are typically delivered either via hardware or software. Both can capture sensitive information and result in serious consequences for both users and organizations. Here are some of the most common types that your organization should be aware of.
API-based keyloggers
Considered to be the most popular type used by threat actors, API-based keyloggers take advantage of a user’s keyboard API to intercept all keystrokes. Threat actors can see each keystroke made by a user, and store that information in their own system. This software is typically installed on a user’s device through malicious webpages or code embedded on poorly secured web browsers.
Hardware keyloggers
Hardware keyloggers are compromised keyboards that have a built-in component used to track and record a user’s keystrokes. While far less common than software-based versions, hardware keyloggers can be harder to detect, making them an appealing option for threat actors. These devices store keystroke records directly on the malicious hardware, meaning the threat actor must retrieve the physical keyboard to access the record of keystrokes.
Kernel-based keyloggers
Kernel-based keyloggers target the core of a user’s computing system to gain administrator privileges. The core of a computer’s operating system is also known as the kernel, hence the name of this type of keylogger attack. Since kernel-based keyloggers can hide with relative ease in your computer’s operating system, they can be very hard to detect and remove. Once installed, they give threat actors access to all keystrokes as they’re processed by the operating system.
Keylogger attacks over time
Originally intended to enable companies to gauge employee device usage or help IT personnel solve issues, keyloggers have evolved to become a malicious tool.
While hardware and software-based versions have been the dominant form of keylogger attacks in recent years, the rise in usage of mobile devices and tablets has resulted in the emergence of mobile-based keyloggers. Going beyond recording keystrokes, some mobile keyloggers can access old messages, reveal geolocation, tap into microphones, and more.
Keyloggers can capture login credentials, sensitive company data, and more. For this reason, this form of malware should be top-of-mind when building your cybersecurity defenses. Unfortunately, they can be difficult to detect.
How to detect and prevent keylogger attacks
Keylogger attacks are constantly evolving, making it difficult for organizations to implement agile cybersecurity solutions that can account for these changes. However, there are cybersecurity solutions that every organization should adopt to protect yourself.
Use multifactor authentication (MFA)
Multifactor authentication adds an additional layer of security to your accounts, requiring at least two forms of verification before you can log in. In addition to a username and password, the additional form of verification is usually a PIN code, fingerprint scan, or security questions. While hackers can bypass MFA, the security measure helps prevent hackers from accessing your account in the event your password is compromised.
Invest in user awareness training
Human behavior is the top reason for data breaches and the #1 vulnerability to your organization’s cybersecurity. When users click a malicious link or download a malware-laden attachment, they can enable keylogger malware to quickly infect their system and create the opportunity for further compromise throughout an entire network.
To protect employees, you should adopt security awareness training that teaches users how to spot and handle cyberthreats, as well as maintain good cyber hygiene practices. . While classroom and generic instruction can provide benefits, look for more effective user awareness training programs that give users personalized, automated, and real-time instruction as they need it.
Adopt email security with anti-malware technology
Email is the top vector for cyberthreats and the #1 channel for distributing malware, a reason organizations should adopt email security with anti-malware capabilities. Traditional solutions like secure email gateways (SEGs) afford protections against known threats such as malware with recognized signature; however, SEGs can’t defend against the unknown cyberthreats including those used in zero-day exploits.
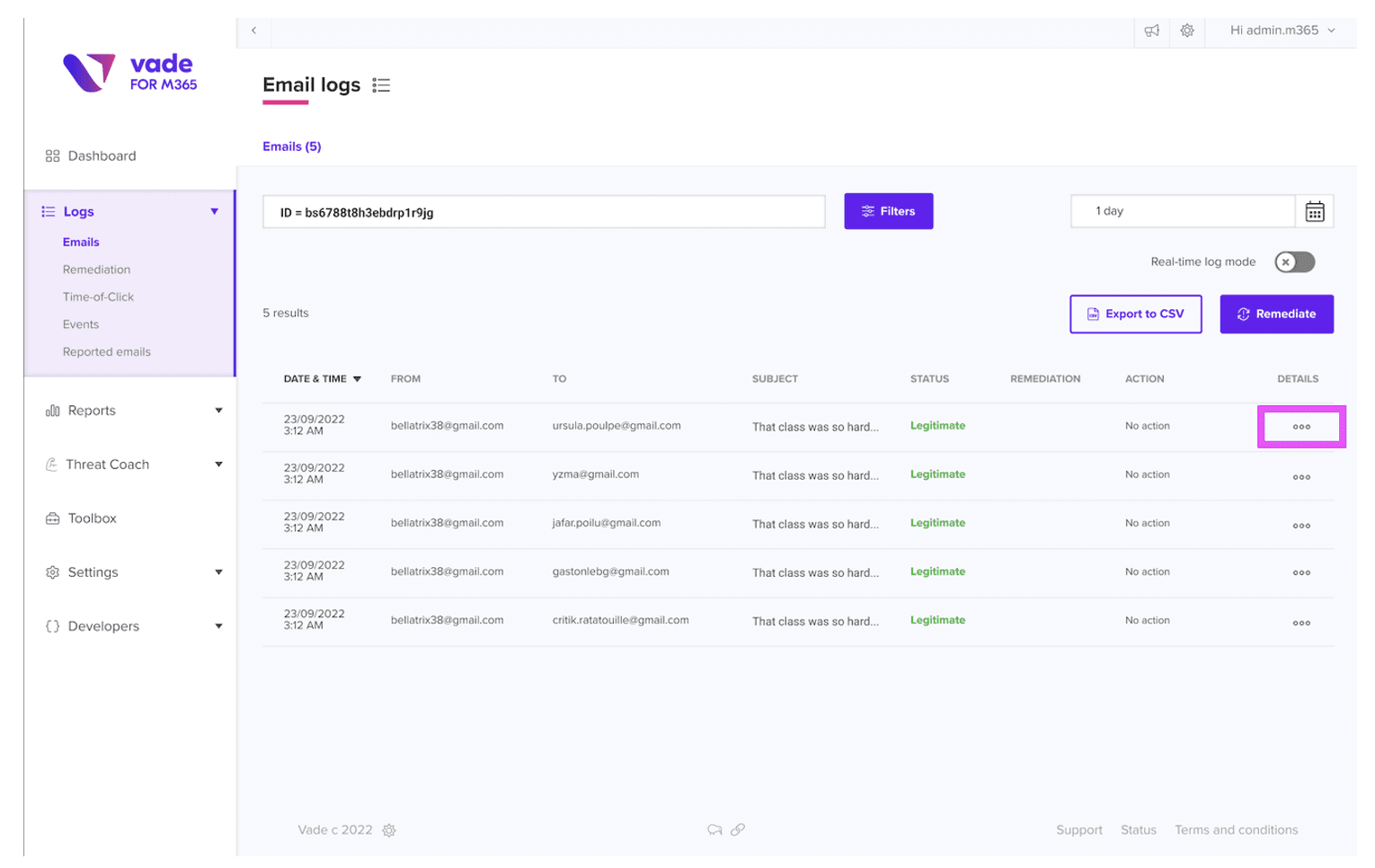
With more than 450,000 new malware variants and potentially unwanted applications introduced daily, you should look to adopt email security solutions that provide integrated, AI-powered threat detection and response. These solutions enable your organization to filter for all types of malware threats, including those not yet seen in the wild. They also block and remediate malware threats transiting your internal network.
Vade offers an AI-powered anti-malware solution that combines machine and human intelligence to detect and neutralize today’s most advanced and dynamic malware variants, including polymorphic and environmentally aware malware. Email security with anti-malware capabilities, together with the other measures detailed in this article, can help keep your organization protected from compromise.