Defending against email spoofing
Adrien Gendre
—November 05, 2020
—3 min read

Email spoofing is a technique for forging an email header to trick recipients into believing a sender is a familiar brand or acquaintance. It’s a critical element of both phishing and spear phishing attacks that can be extremely difficult for users and even sophisticated email filters to detect.
What is email spoofing?
Email spoofing exists on a continuum of sophistication. While some forms of spoofing are quite simple, others require a high degree of skill. There are three main types of spoofing attacks along this spectrum:
Display name spoofing
This is a simple but effective approach to email spoofing in which the sender’s name is spoofed but the email address is not. While a trained user might notice the discrepancy between the display name and the email address, hackers are counting on untrained users who will focus on the display name and not the email address.
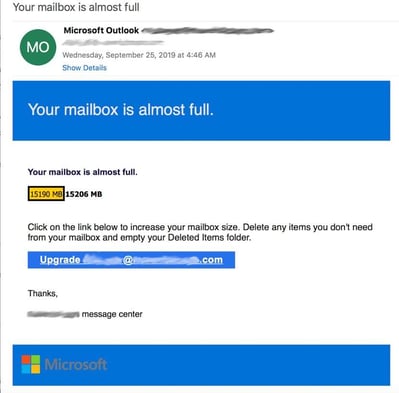
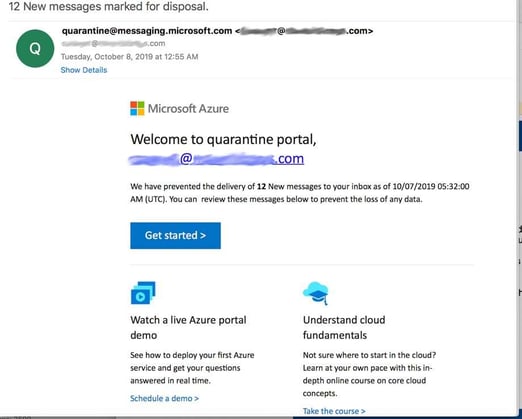
Here’s how display name spoofing works: You get an email from the display name “Microsoft Outlook,” but the email address is xyz22@gmail.com. The attacker is working under the assumption that many busy people won’t check the sender email address carefully—they often don’t.
Display name spoofing is especially effective on mobile because although the sender’s name is always visible on mobile, the email address often is not. This is true for both Microsoft Outlook and Gmail. Mobile users are also more likely to be on-the-go and therefore distracted than desktop users. According to Verizon, mobile users are more susceptible to spear phishing and email spoofing on mobile due to both user distraction and mobile app design.
Another tactic in display name email spoofing is to use an email address as the display name. This distracts the user from looking at the sender’s real email address and adds an extra layer of legitimacy to the email. In the below example, the hacker uses a Microsoft email address as the display name.
When combined with social engineering, display name spoofing can trick people into taking actions they otherwise wouldn’t. For example, the attacker will research the target and use known facts to establish trust before making a request. This social engineering tactic is often used in spear phishing, also known as business email compromise and CEO fraud, in which a hacker impersonates a high-level executive and requests that an employee send a wire transfer.
Exact domain spoofing
With the right tools, an attacker can send a phishing email that appears to come from a legitimate domain. For example, an attacker could send an email that appears to come from support@bofa.com, a legitimate Bank of America email address. Except, it doesn’t actually come from that address. It’s a phishing email designed to get you to click on a URL that sends you to a spoofed webpage that looks like www.bofa.com.
Fortunately, exact domain email spoofing is less common than it used to be, thanks to the Sender Policy Framework (SPF) and Domain Keys Identified Mail (DKIM). Once incorporated into DNS settings, SPF or DKIM prevent unauthorized use of domain names for spoofing attacks.
Cousin domains
A cousin domain is close to and sometimes even indistinguishable from a legitimate domain. This spoofing attack technique might involve using the .co domain extension instead of .com or by adding or subtracting a letter or word from the URL.
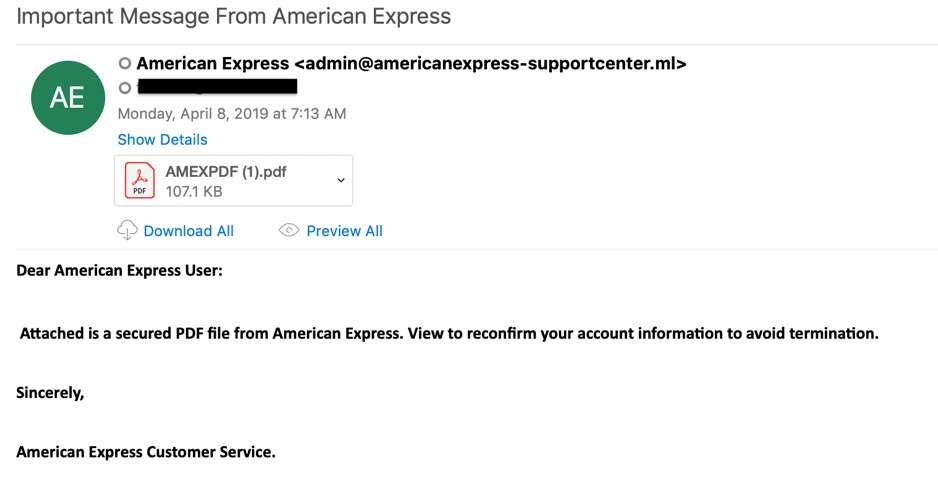
For example, let’s say your company is called Maine Express and has the domain maineexpress.com. A spoofer could register the domain mainexpress.com or maineexpresss.com and fool at least a portion of email recipients. Or they could add an an additional but plausible word to URL, such as “global,” making it maineexpressglobal.com and so forth.
How to stop email spoofing
Though some spoofing attacks are extremely hard to detect, many are easy to spot, and user awareness training can empower your employees to make a difference. Establishing clear policies about processes like sending wire transfers also helps mitigate the risk of business email compromise, CEO fraud, and other spear phishing attacks. To counter cousin domains, some businesses deliberately buy all similar domains. This has the added benefit of reducing the risk of trademark infringement.
Finally, advanced email security solutions can quickly analyze inbound emails for signs of email spoofing and other anomalies. Vade for M365 analyzes email headers to determine if the display name and email address are consistent with the company’s entity model. It also adds an SPF-like layer into the email filtering process that spots unauthorized use of legitimate domain names and cousin domains.
The solution also looks for revealing inconsistencies in email structure and content, including words and phrases commonly used in business email compromise. If spear phishing is suspected, a customizable warning banner is placed inside the email alerting the user to a suspected spoofing attack.




