Email Security Best Practices: Safeguarding Your Digital Communication
Todd Stansfield
—December 28, 2023
—8 min read

Email is a primary channel for communication and collaboration in the workplace.
It also remains the top vector for cyberthreats.
According to Gartner’s Market Guide for Email Security 2023, approximately 70% of organizations use cloud-based email platforms, which lack the necessary security features to protect against advanced cyberthreats. While integrated, third-party email security solutions can secure these vulnerabilities, they make up only 5% of the marketplace. That leaves many organizations vulnerable to compromise.
Email security isn’t a binary measure—it’s not a matter of simply turning it on and being protected. Implementing a solution doesn’t necessarily limit your risk of compromise. Effective email security calls for adopting the right set of technologies and operational procedures for more complete protection.
In this post, we examine email security best practices that will allow you to better protect your users, clients, and business from modern cyberthreats

Understanding the importance of email security
Gone are the days when the Nigerian Prince scam characterized the quality and sophistication of most email threats. The infamous phishing attack symbolized an age when threats were indiscriminate and overtly obvious compared to today’s standards.
The modern threat landscape has drastically changed to deploy highly advanced, convincing, and targeted attacks at scale.
Phishing emails use personalized information and abuse legitimate services to make attacks harder to detect while appearing more credible. Business email compromise (BEC) scams leverage in-depth research on a victim, such details about their current role or background, to coerce them into taking a compromising action. Cybercriminals may use hacked accounts to hijack existing email threads, impersonate legitimate senders, and distribute threats that prey on trusting targets.
The lines between malicious and legitimate content can seem indistinguishable. Unlike the days of the Nigerian Prince, hackers are engineering campaigns that are far more convincing and targeted. And the results show. The cost of a data breach has reached an all-time high, averaging $4.45 million (USD) globally, according to IBM Cost of a Data Breach Report 2023. For businesses with 500 or fewer employees, that figure totals $3.31 million (USD).
This illustrates the importance of email security, a vital field in cybersecurity that protects digital communications and accounts. Email security combines a variety of technologies, practices, and procedures.
While several types of email security threats exist, below are the most common and concerning types:
- Phishing: Phishing is a common email security threat where attackers impersonate well-known, established brands to deceive recipients into clicking malicious links, scanning QR codes, or downloading malware-laced attachments. It is a general type of attack, being sent to many mailboxes and without personalizing the content for the recipient. Phishing can result in credential harvesting, malware infections, account takeovers (ATO), and more.
It remains the most effective cyberthreat by victim count, according to the Internet Crime Complaint Center. The IC3 received 300,000 complaints from victims in 2022 alone. Meanwhile, Vade has detected a record number of phishing threats in 2023.
- Spear phishing or BEC: Spear phishing, often referred to as Business Email Compromise (BEC), is a highly targeted cyberattack. Spear phishers impersonate a legitimate person or vendor known to the victim. Spear phishing attacks don’t usually contain malicious links or attachments, especially in the first email. Rather, they use textual content, research on a victim, and social engineering techniques to manipulate their intended targets into taking a compromising action, usually financial in nature. This includes transferring funds to a fraudulent account (wire transfer fraud), sending tax documents to hackers (tax fraud or W2 fraud), purchasing gift cards in bulk (gift card fraud), and more.
Spear phishing attacks are the costliest cyberthreat. Reported damages from BEC reached $2.7 billion (USD) in 2022, according to the IC3. Equally concerning, the number of BEC attacks continues to climb. According to Verizon’s Data Breach Investigation Report, BEC attacks have almost doubled in 2023 compared to the previous year.
- Email-based malware: While malware poses a threat from several vectors, email remains the top channel for distributing it, including ransomware. This type of email threat typically uses an attachment containing malware that infects the victim’s device once downloaded. Malware-laced attachments most often take the form of Microsoft Office documents, according to Verizon. Some email-based malware attacks may instead contain a malicious link that redirects the victim to a phishing page, which delivers the payload.
- Man-in-the-middle (MitM) attacks: MitM attacks occur when hackers intercept or eavesdrop on communications between two legitimate parties. A common MitM attack occurs when hackers apply phishing techniques to harvest credentials from victims. They’ll do so by initiating an authentication request from an application or website, and if the authentication takes place using the same communication channel, they’ll insert themselves in the middle (hence the name) and steal the credentials. Logging in via email address or intercepting SMS messages are two common attack channels. Hackers then use the harvested credentials in real-time to login to a legitimate service or bypass security mechanisms like multifactor authentication (a technique known as an MFA bypass).
- Spam: Spam is unsolicited and often unwanted emails sent in bulk to many recipients. While spam isn’t inherently malicious, it can clutter mailboxes, consume network resources, and be used to deliver malicious content, including phishing links.
8 essential email security best practices
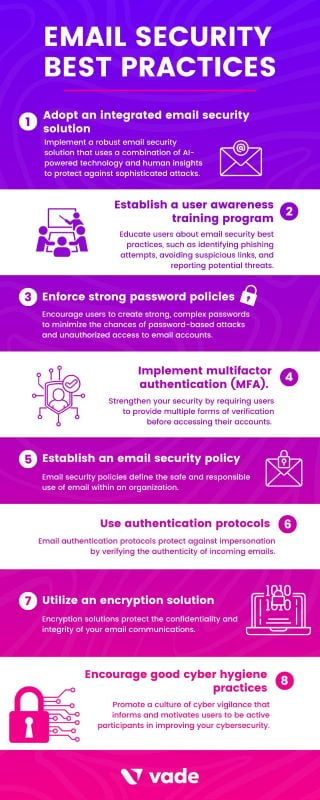
As mentioned previously, secure and effective email security calls for the right set of solutions and operational procedures. To strengthen your posture, adopt the best practices below and make them an ongoing priority for your business.
1. Adopt an integrated email security solution
Integrated email security solutions are widely regarded as providing the best protection against modern email threats. Respected institutions such as Gartner recommend businesses adopt this technology to supplement the native features of their email platforms and replace traditional solutions such as secure email gateways (SEGs).
While SEGs offer security benefits, they also carry important limitations. Unlike integrated solutions, SEGs sit outside the internal network, which means they disable the native security features of email platforms and leave them vulnerable to internal and insider threats. Additionally, SEGs are also time-consuming and difficult to configure and deploy, and they’re often susceptible to threats that are unknown to email filters that use reputation- and signature-based detection. This illustrates the importance of adopting a third-party email security solution.
When shopping for a solution, look for those that provide:
- AI-powered protection. AI algorithms such as Machine Learning, Natural Language Processing, and Computer Vision can provide effective protection against all types of advanced email threats, including those that are new or emerging.
- A single, unified interface for managing email security. A unified interface provides greater visibility and efficiency for administrative tasks such as remediating user reports. Such an interface should offer the coveted ‘single pane of glass’ view that helps admins gauge security status at a glance.
- Robust features for incident response and threat detection. Solutions that offer automatic remediation improve security by immediately removing potential threats post-delivery based on new intelligence. Meanwhile, assisted remediation capabilities enable admins to remediate threats across their users or tenants with a single action, saving precious time.
- Simplicity and ease of use. Solutions with intuitive, user-friendly, and automated features can minimize “time on tool” and make IT and security teams more productive.
2. Implement phishing awareness training
Users are the greatest weakness in your attack surface. Phishing awareness training, however, can make them a valuable line of defense. This training educates users on how to identify common email threats and report them to administrators for remediation. Among other important behaviors, awareness training teaches users how to recognize the signs of spoofing and avoid clicking links or downloading attachments from unknown or suspicious senders.
When choosing a solution, favor those that offer the features below:
- Personalization. Context plays an important role in improving behavior. Training tailored to a user’s role and common email interactions can achieve better results than generic instruction.
- Automation. Automated training programs eliminate the need for human intervention. They also enable education to be delivered on-demand via computer simulation.
- Real-time administration. This type of education doesn’t schedule training in advance. It administers instruction at the time of need. Even better, some solutions automatically deliver training when users encounter a phishing threat.
3. Enforce strong password policies
Compromised accounts pave the way for effective phishing or BEC attacks. Password policies can combat the tendency of users to create weak passwords or reuse them across applications.
To create a strong password policy:
- Require users to set long and unique passwords. The National Institute of Standards and Technologies (NIST) recently concluded that length is a more important factor than complexity for password strength. Length prevents hackers from breaching accounts via brute force attacks (when hackers attempt to guess a password combination manually or with the assistance of technology). At the same time, requiring users to set complex passwords increases the likelihood users write them down or store them on electronically in an insecure manner.
- Limit incorrect password attempts. NIST also recommends limiting the number of incorrect attempts a user can make when attempting to login. This also protects against brute force attacks.
- Develop a list of unacceptable passwords. NIST recommends developing and enforcing a list of unacceptable passwords that includes dictionary terms, specific names, and breached credentials. This limits the chances hackers can gain access.
4. Adopt multifactor authentication (MFA)
Like effective password policies, MFA makes it harder for hackers to compromise and manipulate legitimate accounts. MFA requires users to authenticate their identity through multiple factors before accessing email or other applications.
Like most cybersecurity solutions and practices, not all forms of MFA provide equal protection. To maximize your security, the Cybersecurity & Infrastructure Security Agency (CISA) recommends adopting FIDO/WebAuthn authentication, which prevents users from logging into a phishing page. If this isn’t an option for your business, CISA recommends using app-based, SMS, or voice MFA as an alternative measure.
5. Establish an email security policy
Along with user awareness training, an email security policy addresses the human element of your overall posture. Email security policies define the safe and responsible use of email within an organization. They establish rules and guidelines for how users should handle sensitive information, adhere to security protocols, and other factors.
When developing your email security policy:
- Create the policy using an existing template from a reputable organization, like the SANS Institute.
- Make it easy for employees to locate and access the policy.
- Make it digestible and easy to understand.
- Incorporate the email security policy into new hire orientation and onboarding programs.
- Promote the policy in formal and informal organizational meetings.
- Allow employees to review and formally acknowledge the policy initially and any time significant updates are made to it.
6. Use authentication protocols
Email authentication protocols protect against impersonation by verifying the authenticity of incoming emails. They include Sender Policy Framework (SPF), Domain-Keys Identified Mail (DKIM), and Domain-based Message Reporting and Conformance (DMARC). Adopting these protocols provides protection against email spoofing, phishing attacks, and domain impersonation.
NIST provides detailed recommendations for implementing SPF, DKIM, and DMARC. You can also find many resources and vendors to assist you in adopting DMARC, a free and open standard. Many organizations have yet to implement and enforce it.
7. Utilize an encryption solution
Encryption solutions protect the confidentiality and integrity of your email communications. These solutions make digital communications unintelligible to unintended recipients, who lack the decryption key. At a time when MitM attacks are increasingly common, encryption keeps correspondence and other information secure.
According to Gartner’s Market Guide to Email Security 2023, about 40 percent of organizations have adopted an encryption solution. This low number is due in part to usability issues. However, this statistic is increasing with the emergence of newer end-to-end solutions that improve ease of use.
8. Encourage good cyber hygiene practices
Promote a culture of cyber vigilance that informs and motivates users to be active participants in improving your cybersecurity.
To encourage good cyber hygiene practices, focus on the initiatives below. Note that these should supplement your user awareness training programs:
- Encourage users to physically secure their workstations when left unattended.
- Educate users on the safe handling of sensitive information.
- Discourage the practice of Shadow IT (using applications or web services that have not been sanctioned by IT).
- Discourage the use of personal accounts of corporate devices.

FAQs
- Why is email security important for businesses?
Email remains the primary channel for cyberthreats and top source of security incidents and data breaches. The absence of email security puts organizations at risk of financial losses, reputational damage, regulatory violations and penalties, and legal consequences. Approximately 20% of organizations that experience a data breach pay at least $250,000 (USD) in regulatory fines. Email security provides necessary insurance for continued business continuity.
- What are common email security threats?
Common email security threats include phishing, spear-phishing, and malware attacks. These email-based threats deliver malicious links or attachments or use social engineering techniques to compromise victims. They require users to take at least one compromising action, such as clicking a link, downloading an attachment, or complying with a sender’s demands.
- How can I protect my organization from email phishing attacks?
To protect your organization from email phishing attacks, adopt an integrated, third-party email security solution, provide phishing awareness training to users, and implement email authentication protocols (including SPF, DKIM, and DMARC). It’s also important to implement policies for email security and passwords and to adopt additional security measures such as MFA.
- What role does employee training play in email security?
User awareness training plays a crucial role in email security. Today, human error accounts for nearly three in every four data breaches, according to Verizon’s Data Breach Investigations Report. Training helps users recognize the warning signs of common cyberthreats and teaches them safe practices, such as inspecting emails for the signs of spoofing, avoiding downloading attachments from unknown senders, and other behaviors. Employee training reduces the chances of a security incident, and consequently, a data breach.