Phishers’ Favorites 2022 Year-in-Review: Google Phishing Increases
Todd Stansfield
—March 07, 2023
—2 min read
Today, Vade released our annual Phishers’ Favorites Year-in-Review report. For the report, Vade analyzed 274,636 phishing pages from January 1, 2022 to December 31, 2022. The Phishers’ Favorites 2022 Year-in-Review report examines the most impersonated brands and industries of the year and uncovers the phishing trends that defined 2022.
Facebook headlines as the most impersonated brand amid a year of uncertainty
For the second consecutive year, Facebook was the top impersonated brand, edging out Microsoft. With more than 25,000 unique branded phishing websites—Facebook represented nine percent of phishing URLs detected.
Facebook was the fourth most impersonated brand in H1 2022, but its H2 performance pushed it to the top of the leaderboard for 2022. The sharp increase in phishing websites impersonating Facebook coincided with a tumultuous second half of the year for the company. Reports of slowing growth in active users and advertising revenue led to a marked decline in the company’s stock price and substantial layoffs.
Google makes a surprise appearance as third most impersonated brand
Google, which finished 2021 in the #28 spot of most impersonated brands, made a surprising leap in 2022 to end the year at #3. The cloud provider accounted for a 1,560% increase in unique phishing pages, with 19,695 phishing URLs.
Microsoft finished #2 on the list for the second consecutive year. Nine percent of all phishing pages detected by Vade in 2022 impersonated Microsoft. Microsoft and Google dominated the cloud sector, surpassing the combined total of unique phishing pages impersonating all other cloud brands (42,226 vs. 38,893).
The popularity of both brands in phishing attacks follows a rise in demand for their productivity software. Microsoft 365 and Google Workspace are the #1 and #2 most popular productivity suites in the world, respectively. The report reveals that productivity suites have become an attractive target for phishers, creating more opportunities to exploit users before and after an initial compromise, as well as distribute malicious links and files through new channels, such as instant messaging tools.
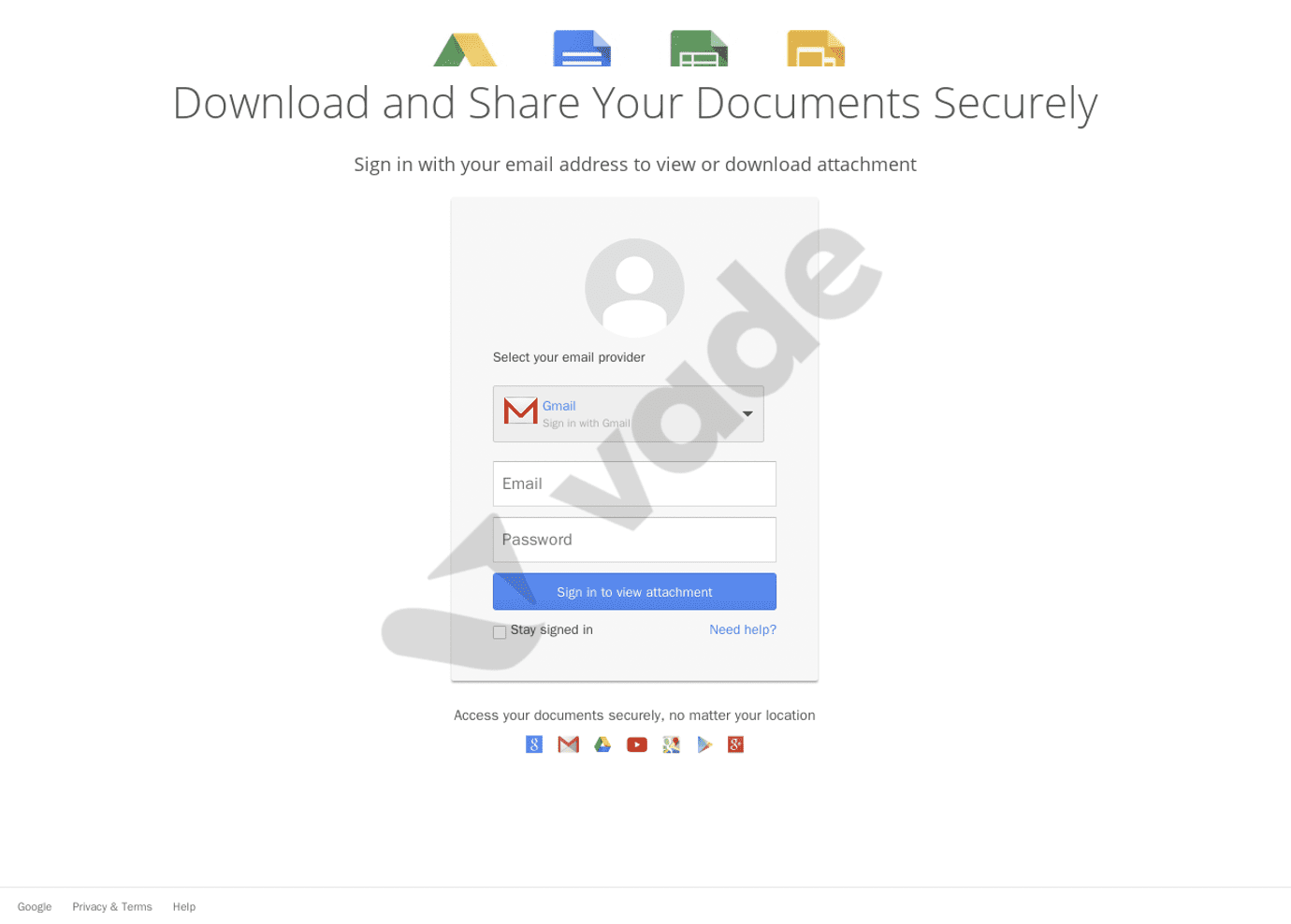
Google impersonation detected by Vade
Financial services was the most impersonated industry
Representing 34% of all phishing pages, financial services was the most impersonated industry of the year. PayPal, MTB, Crédit Agricole, and La Banque Postale led the industry, each securing a spot in the top 10 of most impersonated brands, while seven brands finished in the overall top 20.
Cloud, the second most impersonated industry of 2022, represented 23 percent of all phishing pages, followed by social media and internet/telco at 16%.
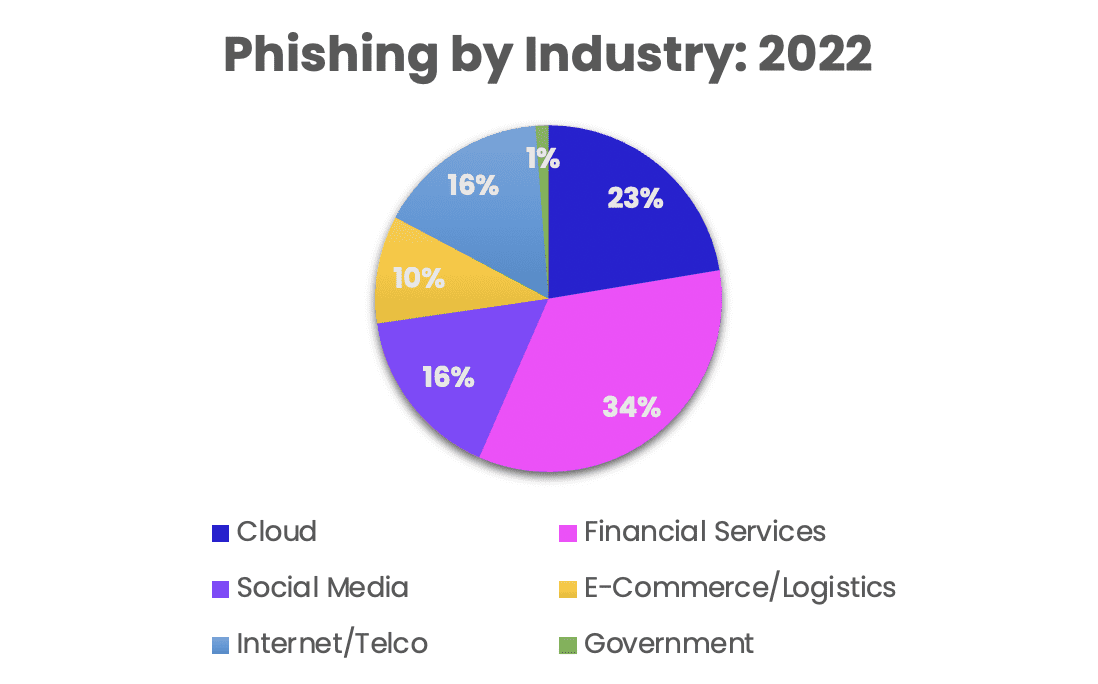
Phishing volumes by industry in 2022
Phishing volumes increase significantly across industries
2022 accounted for a significant increase in phishing pages, which rose 48% year-over-year. Excluding social media, every industry experienced a sharp rise in volumes. Internet/telco saw the largest increase (111%), followed by cloud (77%), ecommerce/logistics (59%), financial services (46%), and government (26%).
2022 phishing trends
This year’s Phishers Favorites Year-in-Review report uncovers several notable phishing trends, including:
- Phishers opt for more targeted attacks. As public awareness of common phishing techniques continues to increase, hackers are deploying more targeted attacks rather than indiscriminate, broad scale campaigns.
- Phishers exploit current events. Hackers continue to take advantage of current events to engineer attacks and exploit victims.
- Phishers abuse legitimate services. Hackers are weaponizing legitimate services to bypass detection and scale phishing attacks, which Vade researchers expect will continue in 2023. These attacks exploit the legitimate servers, IP address, and domain name of websites.
To see the full analysis from the Phishers’ Favorites 2022 Year-in-Review, download the eBook.




