Top 6 Phishing Trends of 2020
Adrien Gendre
—November 12, 2020
—4 min read

Phishers are evolving and taking their attacks to new heights. While the ultimate goal of phishing remains the same, the top targets of spoofing are changing, and the methods of bypassing email filters are more sophisticated than ever. These are the top six phishing trends we’ve seen at Vade so far in 2020.
1. COVID-19 created a long-term opportunity
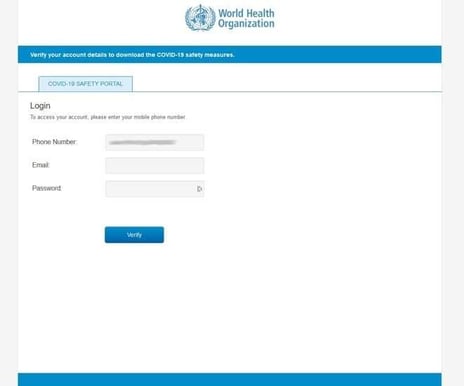
Vade first reported COVID-19 phishing emails in March 2020. What at the time seemed like a passing phishing trend has morphed into an eight-month onslaught of pandemic-focused attacks. The first COVID-19 themed emails exploited the fear and uncertainty of the virus and resulting global lockdowns. From the World Health Organization (WHO) to state and federal health agencies, it seems everyone got spoofed at the beginning of COVID.
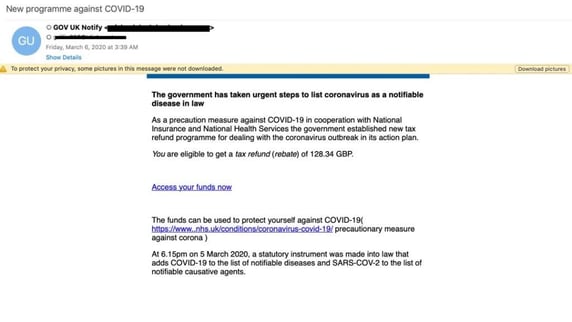
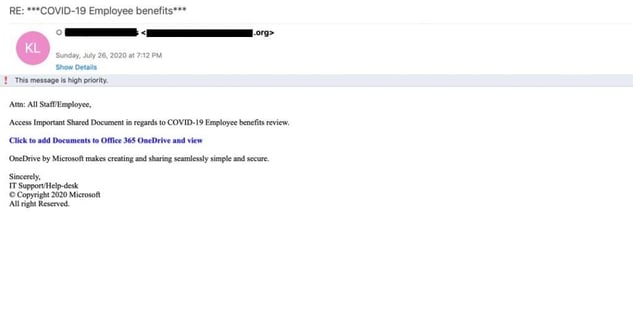
As the pandemic proceeded to draw out, the public became more educated about the threats and hackers changed course. With layoffs skyrocketing and surviving employees working from home in never before seen numbers, hackers pounced on the opportunity to exploit a workforce in flux.
Phishing trends during the second half of the year, phishing examples ranged from fake internal emails touting new health benefits to run-of-the-mill, password reset emails that exploited the physical gulf between employees and the IT department.
Regardless of the theme, it’s clear that COVID-19 phishing is far from over. As the world drifts in and out of lockdown mode and businesses struggle to keep afloat, hackers will continue to adjust their methods to find a way to exploit the situation.
2. Ransomware is back and badder than ever
Ransomware gangs were busy in 2020. According to a recent report by Kroll, ransomware was the most observed threat in 2020. According to Kroll, Ryuk, Sodinobiski, and Maze were the most observed forms of malware in 2020, representing 35 percent of all attacks and 26 percent were delivered via phishing emails.
Ransomware increased in nearly all categories in 2020. According to CyberEdge Group, 62.4 percent of organizations were affected by ransomware in 2020, up from 56.1 percent in 2019. The cost of ransomware increased from $11.5 billion to $20 billion, and 57.5 percent of businesses affected by ransomware paid the ransom, compared to 45.1 percent in 2019.
MSPs were hit particularly hard by ransomware in 2020. According to a joint survey from Coveware and NinjaRMM, 57 percent of MSP respondents reported a customer churn rate of 11-20 percent following a ransomware attack. Thirteen percent of MSPs reported a 50 percent churn rate or higher. Of all the ransomware variants reported by MSPs, Cryptolocker, WannaCry, and CryptoWall were the most common.
3. Emotet made its unwelcomed return
The return of Emotet Malware began in July and has yet to slow down as we near the end of 2020. Microsoft sent an alert on July 17 with evidence of a large phishing campaign featuring malicious links and attachments.

In August, Vade detected an anomalous increase in unique Microsoft phishing. As we noted in our Q3 Phishers’ Favorites report, Microsoft typically sees around 240 unique phishing URLs on peak days, but the number spiked to 846 on August 21.
In September, Australian, Japanese, French, and Italian security agencies sent out urgent alerts about Emotet activity. Around the same time, Vade detected a massive increase in Microsoft phishing URLs: 1,799 on September 1 and 1,151 on September 21. Continuing into October, Vade detected ongoing waves of Emotet activity, particularly on weekdays when workers are glued to their inboxes.
Early this month, an HP Inc. report revealed that Emotet emails surged 1,200 percent from Q2 to Q3 2020. Microsoft-themed Emotet campaigns continued, with malicious Word docs and phishing emails with a Microsoft Word update as the lures.
One of the top phishing trends seen in Emotet emails is thread hijacking. Thanks to tools like Outlook scraper, which are deployed at the point of an Emotet infection, hackers inject themselves into email threads and impersonate colleagues and connections to spread more infections via phishing links and attachments, including password-protected .ZIP files.
Are your users still clicking on phishing links? Learn about automated phishing awareness training.
4. More phishing attacks are sent at low volumes
The mass phishing campaigns of the past are becoming more targeted and sent at lower volumes. In the past, a single phishing email might be sent to hundreds of recipients and included generic greetings such as “dear customer” or even a simple “hello”. In 2020, most phishing campaigns detected by Vade were sent at much lower volumes.
Why the change? Mass phishing waves are easier to detect than low-volume attacks, indicating that phishers are getting smarter about picking their targets. One thing that has changed is that in 2020, attacks were not as highly targeted as they were in 2019. One email, for example, might be sent to 20 or even 50 employees within the same company
5. Hackers are hiding behind file-sharing services
SharePoint, OneDrive, Dropbox. Workers receive shared-file notifications from these well-known applications on a daily basis. In 2020, hackers increasingly exploited the credibility of these services to conceal both their identities and the intentions.
Vade first noticed the rise in file-sharing phishing in 2019, with the majority of phishing examples featuring emails impersonating SharePoint and OneDrive. The latest entrants to this list include WeTransfer and Docusign, two services that saw increased use during COVID-19.
One of the most common and simple techniques of exploiting these services is directing the URL in the email to a phishing page, such as a Microsoft 365 or WeTransfer login page. When the user enters their account credentials, it’s harvested by the phisher. Another technique is to share a legitimate file hosted on a legitimate file-sharing service and burying the phishing link in the attachment. This is effective because many anti-phishing solutions can’t scan links in shared files.
6. Microsoft phishing emails don’t always spoof Microsoft
Microsoft remains the #1 spoofed brand in phishing attacks due to the growing adoption of Microsoft 365. Between Q1 and Q3 2020 , Vade detected 30,608 unique Microsoft phishing URLs. With a set of Microsoft 365 login credentials, phishers have access to a business’s entire ecosystem, from employees’ personally identifiable data, to financials, to customer data.
In 2020, we saw more and more phishing examples in which hackers impersonated a brand other than Microsoft in the actual phishing email and then directed the user to Microsoft 365 to harvest their credentials. Below is a Dropbox phishing email. When the user clicks the “View Transfer” link, they’re directed to a Microsoft 365 phishing page.

The idea behind this technique is to capitalize on both Microsoft’s wide reach and trust ratio. Because of Microsoft 365’s vast user base, there is a very good chance that the recipient is a user and that the user will trust the phishing page rather than question it.
We saw this technique throughout the year. In the below phishing example, the hacker spoofed a notification email from a business’s Zerox scanner. The attachment includes a pre-populated Microsoft form.
Phishing trends in 2020 and beyond
If there’s any good news about phishing it’s that businesses are getting better at user awareness training. Unfortunately, phishers are getting better, too. They’ve even started spoofing phishing awareness training platforms.
If you haven’t already invested in phishing training, it’s time to start. In addition to structured training, users should receive immediate, contextualized training if they click on a phishing link. Vade automates this process with Vade Threat Coach, automated phishing awareness training in Vade for Microsoft 365. Finally, cloud services continues to be targeted by phishing more than any other industry. We expect phishing attacks targeting Microsoft and other top brands on our Phishers' Favorites list to see continued attacks.