Pretexting: 5 Social Engineering Tactics
Adrien Gendre
—June 04, 2020
—3 min read

Pretexting is a form of social engineering used to manipulate victims into divulging sensitive information. Hackers often research their victims in advance of their first conversation. This gives the hacker a sense of the victim’s personal and professional life and assists with establishing the right pretext with which to approach the victim.
Common in spear phishing, or business email compromise, pretexting is typically phase one of a broader scheme to extract information from a victim. Ultimately, it’s an invitation to participate in a crime. It often starts with a friendly “hello” and ends with businesses losing thousands—sometimes millions—of dollars.
Below are five pretexting and social engineering examples detected by Vade:
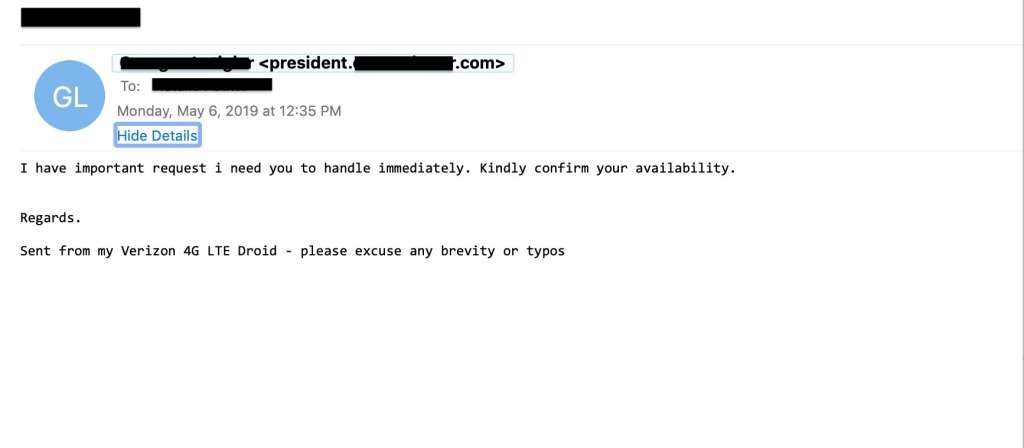
1. Are you available?
Hackers are busy people, so it’s not surprising that they often initiate a conversation by checking on a victim’s availability. “Are you available?” is the pretext a hacker uses to determine if their chosen victim is useful to them and to establish a rapport. It also works to lower the victim’s guard as opposed to immediately making a financial request.
If the victim replies that they are available, another email will follow, possibly with instructions to wire money or purchase gift cards, or maybe just more small talk. If the victims replies that they are in fact busy, out of town, or on PTO, then they likely will not be able to carry out the hacker’s demands. When this happens, the hacker will move on to the next victim on the list.
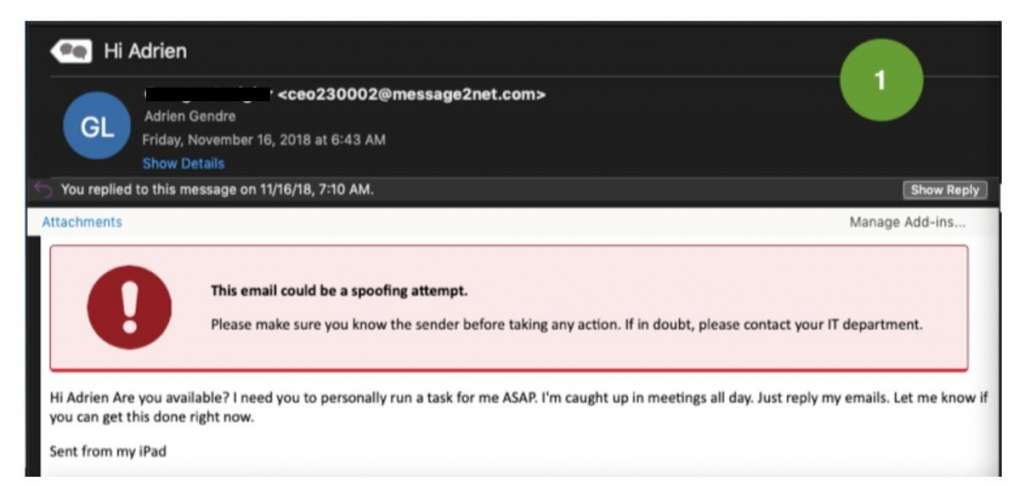
2. I need your help
Impersonating high-profile executives is one of the most common tactics used in spear phishing. It puts pressure on the victim to act quickly and, in many cases, this pressure often causes a lapse in judgment. It’s especially effective against victims who aren’t accustomed to receiving emails from the CEO. Rather than being suspicious, the victim simply springs into action. In the below social engineering tactic–also known as CEO fraud–the hacker puts pressure on the victim by claiming to be in a meeting—incapable of completing the task himself.
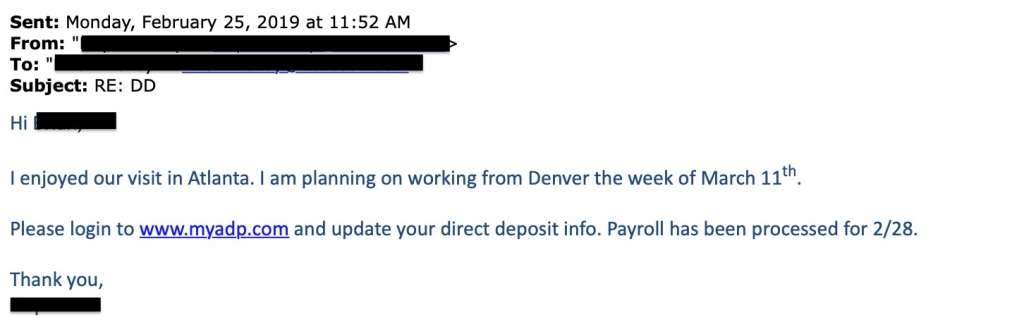
3. Nice seeing you
If the hacker does their homework on both the impersonation victim and the email recipient, they can get a feeling of the relationship that exists between the two. In many cases, the hacker can learn highly specific details they can use as their pretext. In the below example, the hacker has learned of a recent meeting that took place between the impersonation victim and the email recipient. They use this information to create an air of familiarity, which could put the victim at ease for the payroll diversion request that follows.
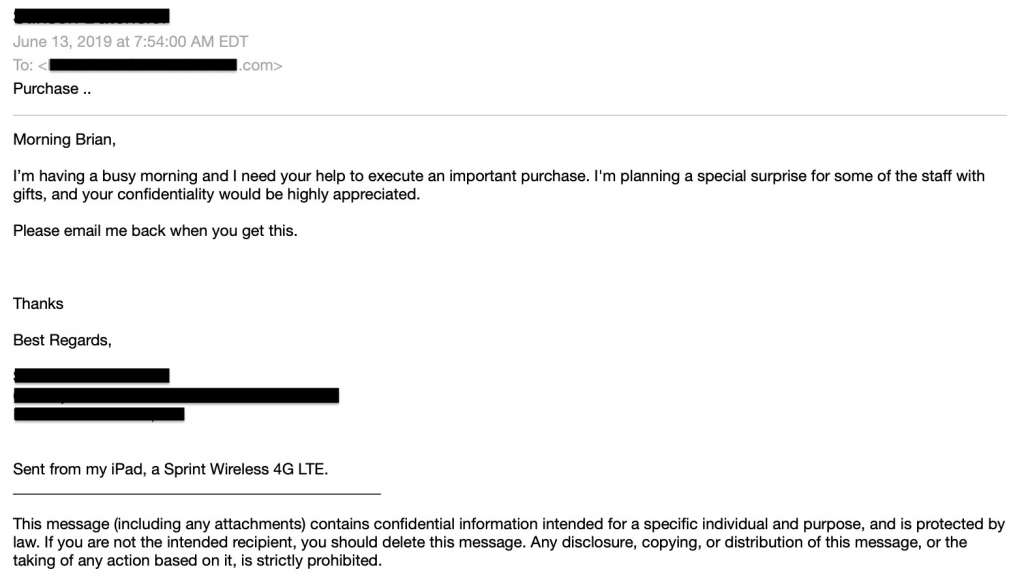
4. I’m planning a surprise
In this example, the hacker informs the victim that they are planning a special surprise for either colleagues or clients, and they need their help in pulling it off. This pretext serves two ends: First, it makes the victim believe they’re doing a good deed, and second, it ensures that the victim will not inform any colleagues or superiors about the request, which gives the hacker time.
Like some of the above social engineering examples, the request also helps the hacker understand if the victim is in a position to help with the request. Again, if the hacker has reached out to the wrong person, they can move on to another target. Often, the hacker will ask the victim for the email address of the best person to contact.
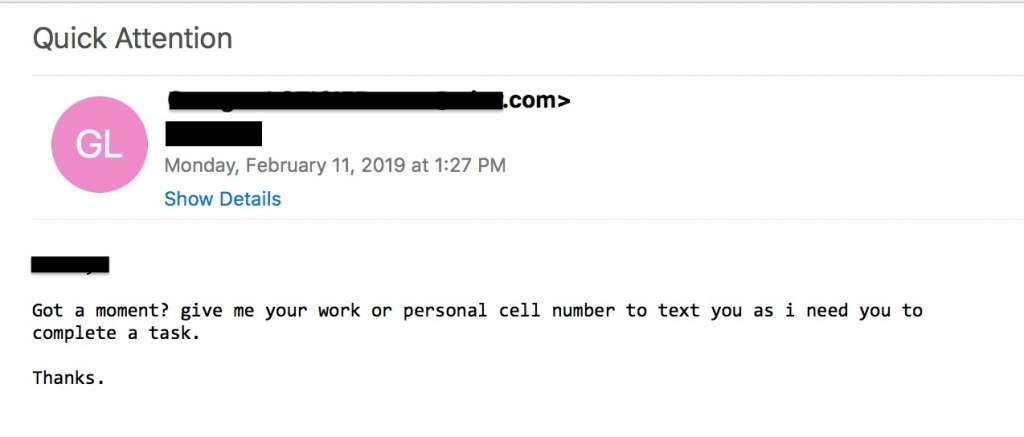
5. Send me your phone number
Because of the prevalence of business email compromise, many businesses require employees to validate wire transfer and other financial transaction requests by phone. This example of pretexting sets the victim up for such a phone conversation with the hacker.
This could also set the victim up for a deepfake. Several high-profile cases of deepfakes were reported in the last year, including one UK case in which a hacker spoofed a CEO’s voice with AI software and defrauded the company out of $244,000. While phishing for a phone number could be used for the purpose of a deepfake, it could also be used for other purposes. Mobile numbers, for example, are often used as proof of identity and to unlock online accounts.
How to prevent pretexting
Pretexting involves impersonation, and to be successful the email must look legitimate. This requires email spoofing. DMARC is the most common form of protection for email spoofing, but it has limitations, including complex and continual maintenance. Additionally, DMARC blocks exact domain spoofing but not cousin domains or display name spoofing, which are far more common in spear phishing attacks, primarily due to the effectiveness of DMARC.
To prevent pretexting, businesses should look toward a more modern approach to email security than DMARC. Anti-spear phishing technology that uses artificial intelligence (AI) analyzes behaviors for signs of pretexting, scanning emails for malicious patterns. Additionally, it can detect anomalies in email traffic and in email addresses, including cousin domains and display name spoofing. Natural Language Processing (NLP), a branch of AI, analyzes language and can decipher words and phrases common in pretexting and spear phishing.
Finally, train your users to spot pretexting by sharing real-life pretexting examples with them. Often, what makes pretexting and spear phishing successful is that users are unfamiliar with the above pretexting tactics and see nothing unusual about the requests they receive. Educate them on the different types of email spoofing and train them to inspect email addresses for signs of cousin domains and display name spoofing. You should also have rules in place about financial transactions, such as validating requests over the phone or in person.




